The Perfect Digital Storm: Why the WEF Ranks Cybersecurity as India's #1 Risk in 2026
702 attacks per minute. 369M in a year. Why the WEF just ranked cybersecurity as the ultimate threat to India’s booming digital economy.
While the world braces for geoeconomic confrontation, India faces a different kind of frontline. With 702 cyber threats detected every minute, the nation's rapid digital leap has created a systemic vulnerability. Here is a deep dive into the threat landscape.
 With 369 million malware detections in a single year, the WEF Global Risks Report 2026 ranks cybersecurity as the foremost threat to India's digital and economic sovereignty.
With 369 million malware detections in a single year, the WEF Global Risks Report 2026 ranks cybersecurity as the foremost threat to India's digital and economic sovereignty.
The World Economic Forum's (WEF) Global Risks Report 2026 paints a stark picture of the near future. Globally, the world is holding its breath over "Geoeconomic Confrontation"—the weaponization of trade, tech, and capital.
But for India, the narrative is chillingly different.
According to the WEF, Cybersecurity is the number one risk facing India in 2026. It has surpassed economic downturns, extreme weather, and even state-based armed conflict.
Why? Because India's greatest triumph—its rapid, unprecedented leap into digital governance (Aadhaar, DBT), digital finance (UPI), and smart infrastructure—has outpaced its cyber resilience. Cybersecurity in India is no longer an IT issue; it is a systemic national security and governance challenge.
Coupled with the recent India Cyber Threat Report 2025 by the Data Security Council of India (DSCI) and Seqrite, the reality on the ground is alarming. Between late 2023 and 2024, India witnessed a staggering 369.01 million malware detections.
That is 702 attacks every single minute.
Here is a deep dive into the anatomy of the threats targeting India, the state-sponsored actors at our digital borders, and what it takes to survive the storm.
The Convergence of WEF's Macro Risks and Micro Realities
The WEF report highlights that cyber risk in India doesn't exist in a vacuum. It acts as a "risk multiplier" alongside other major domestic vulnerabilities:
- The Inequality Multiplier: The WEF lists Income and Wealth Inequality as India's second-biggest risk. When a cyberattack cripples a public service, a regional bank, or a government subsidy portal, it disproportionately harms marginalized, informal workers.
- Public Service Vulnerability: With rapid urbanization and digitization of healthcare (Ayushman Bharat) and finance, the concentration of data creates single-point vulnerabilities. A breach here doesn't just steal data; it erodes the social contract and public trust.
- Geopolitical Spillover: As a key Quad member and a rising global economic powerhouse, India's deep integration into global supply chains makes it a prime target for hybrid warfare, intellectual property theft, and hacktivism.
The Ground Reality: What the DSCI 2025 Report Reveals
While the WEF warns of the impending macro-threat, the DSCI telemetry data provides the forensic evidence.
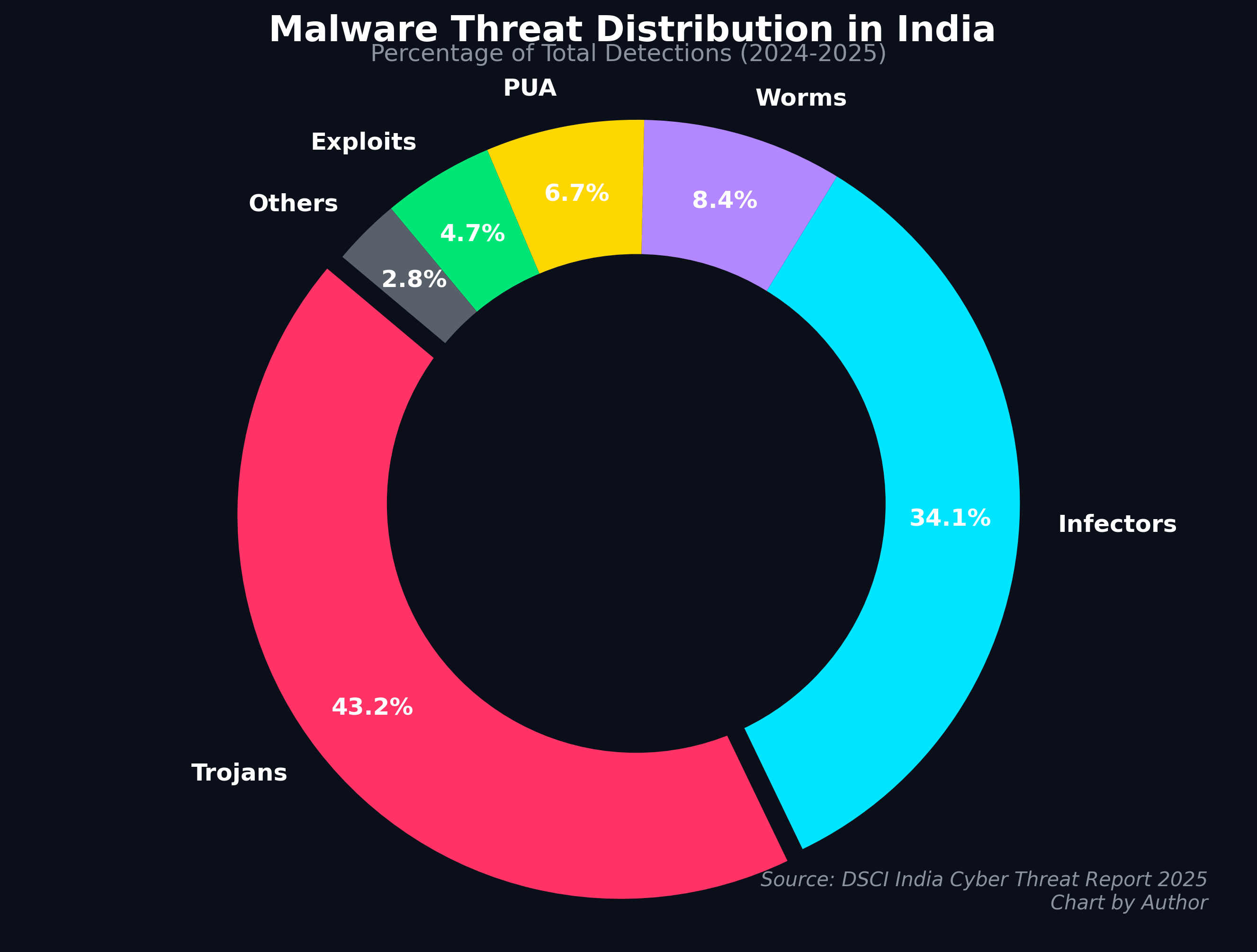 Accounting for over 77% of all detections, stealthy Trojans and system-corrupting Infectors dominate the Indian cyber landscape. This highlights a deliberate shift by cybercriminals away from "noisy" adware toward sophisticated backdoors designed for espionage, data exfiltration, and long-term network persistence.
Accounting for over 77% of all detections, stealthy Trojans and system-corrupting Infectors dominate the Indian cyber landscape. This highlights a deliberate shift by cybercriminals away from "noisy" adware toward sophisticated backdoors designed for espionage, data exfiltration, and long-term network persistence.
- The Cloud is the New Battlefield: A massive 62% of detections occurred in cloud environments, reflecting the rapid migration of Indian businesses to the cloud, often with misconfigured APIs and inadequate workload protection.
- The Rise of Behavior-Based Attacks: Signature-based antivirus is dying. Behavior-based malware detections jumped by 974.6% over the last three years. Attackers are using polymorphic malware and "Living-off-the-Land" (LOLBins) techniques that hide inside legitimate operating system processes to evade detection.
- Tier-2 Cities Under Siege: While tech hubs like Telangana (15% of detections) and Tamil Nadu (12%) are heavily targeted, Tier-2 cities are emerging as massive hotspots. Surat surprisingly led the nation with the highest detection rate (69.34 detections per endpoint), indicating that attackers are hunting for high-value industrial targets with potentially weaker cyber defenses.
- Top Targeted Sectors: Healthcare (21.8%) took the top spot, followed by Hospitality (19.5%) and BFSI (17.3%). Attackers know these sectors hold highly sensitive data and cannot afford operational downtime, making them prime targets for extortion.
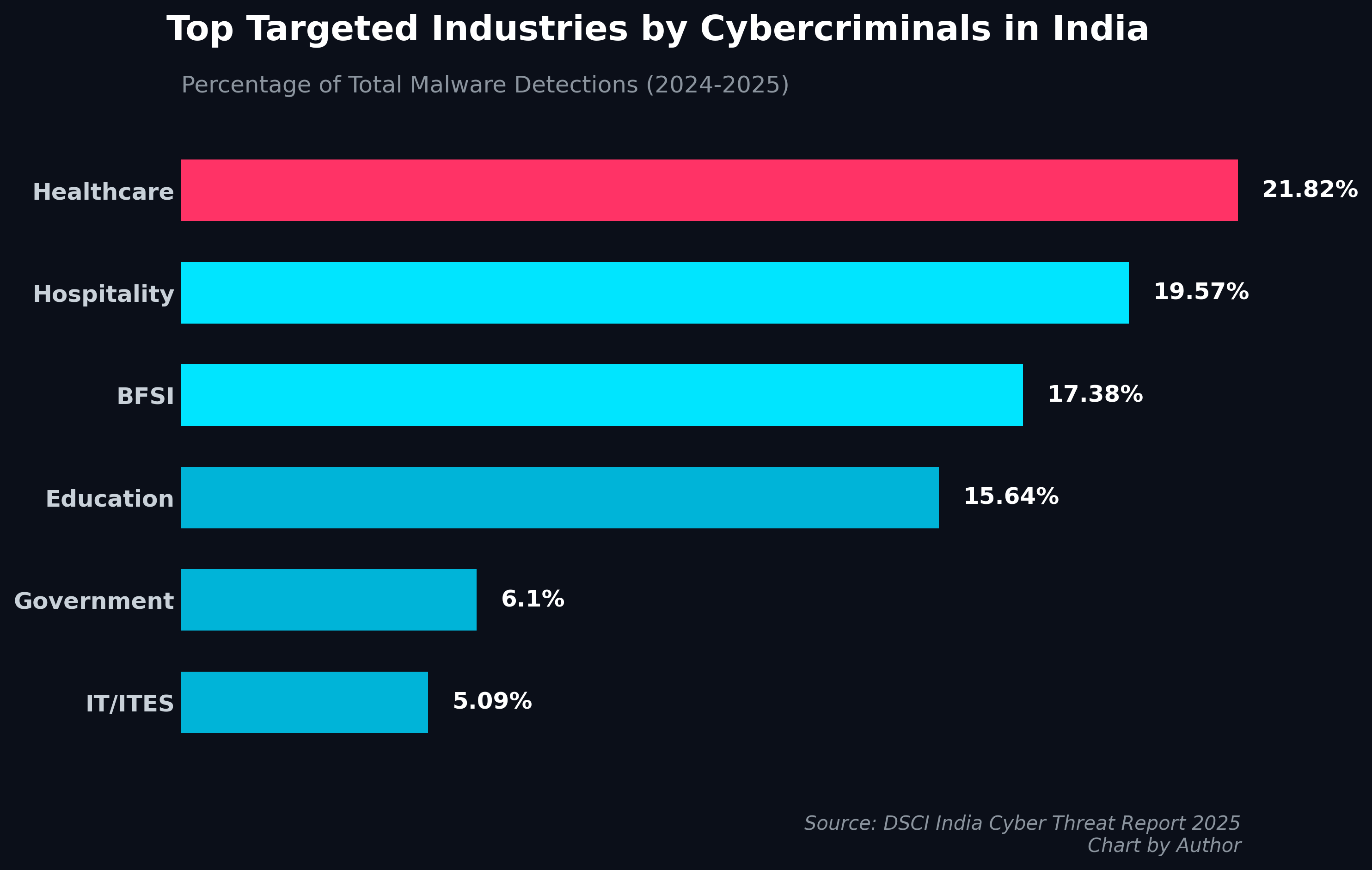 According to DSCI telemetry data covering 8.44 million endpoints, cybercriminals are overwhelmingly targeting sectors that house critical personal and financial data—where operational downtime means life or death, making them highly susceptible to extortion.
According to DSCI telemetry data covering 8.44 million endpoints, cybercriminals are overwhelmingly targeting sectors that house critical personal and financial data—where operational downtime means life or death, making them highly susceptible to extortion.
The Threat Actors: APTs, State-Sponsors, and Hacktivists
The geopolitical tensions mentioned in the WEF report are actively playing out on India's servers. Advanced Persistent Threat (APT) groups from hostile neighboring states, as well as global cyber-mercenaries, are actively running campaigns against India.
1. Pakistan-Linked APTs: The Espionage Campaigns
- APT36 (Transparent Tribe): A notorious state-sponsored group targeting Indian government and defense personnel. The DSCI report highlights their use of the CrimsonRAT, which infiltrates educational and defense networks via spear-phishing to establish remote control and steal data.
- Operation Celestial Force: An ongoing, highly complex campaign targeting the Indian subcontinent since 2018. They utilize malware like GravityRAT and HeavyLift to target both Windows and Android devices of defense personnel, stealing intelligence via deeply obfuscated code.
- Operation FlightNight: A recent campaign targeting Indian government entities and private energy companies. Attackers used a fake "Indian Air Force invitation" to drop a modified HackBrowserData stealer, exfiltrating over 8.8GB of critical defense and energy data via Slack channels.
2. Global and Regional State-Sponsored Actors
- Operation RusticWeb (China/Global overlaps): Targeting Indian government and defense. Notably, this campaign marked a shift from traditional languages (C++) to modern ones like Rust and Golang, making the malware incredibly fast and virtually invisible to legacy antivirus software.
- Operation ShadowCat (Russian-speaking actors): A highly sophisticated cyber-espionage campaign specifically targeting individuals, journalists, and government officials interested in Indian political affairs.
- ShadowPad APT (China-linked): A highly sophisticated multi-module backdoor used in targeted attacks against Indian information systems for data exfiltration.
3. The Hacktivist Surge (The Israel-Palestine Fallout) The DSCI report notes that since the outbreak of the Israel-Hamas war in late 2023, India's diplomatic stance has made it a massive target for retaliatory hacktivism. Over 150 pro-Palestinian hacktivist groups (such as Anon Black Flag Indonesian and The Anonymous Bangladesh) have targeted Indian critical infrastructure with DDoS attacks, website defacements, and data leaks.
Anatomy of the Attacks: How Indians are Getting Hacked
The sophistication of attacks targeting the average Indian citizen and enterprise has evolved beyond simple phishing emails.
 Cybercriminals are heavily targeting Indian citizens via WhatsApp, deploying "RewardSteal" APK malware disguised as urgent government notifications, such as fake traffic violation alerts.
Cybercriminals are heavily targeting Indian citizens via WhatsApp, deploying "RewardSteal" APK malware disguised as urgent government notifications, such as fake traffic violation alerts.
1. WhatsApp APK Malware (The "RewardSteal" Campaign) Cybercriminals are weaponizing trust. Threat actors send WhatsApp messages posing as the Electricity Board, Gas Companies, or even the Traffic Police (e.g., fake Vahan Parivahan apps). They create urgency—"Pay your traffic fine now" or "Update your KYC or your account will be blocked." The attached APK file, once installed, hides its icon and quietly siphons SMS data, banking OTPs, and personal information directly to command-and-control servers.
2. Supply Chain Compromises Attackers are poisoning the well. The DSCI report highlighted the critical XZ Utils (CVE-2024–3094) vulnerability—a near-catastrophic supply chain attack where malicious code was injected into a widely used open-source compression tool, targeting Linux systems globally. Closer to home, popular Indian software installers like Notezilla and Copywhiz were trojanized to steal crypto wallets and browser credentials.
3. Ransomware Targeting Critical Infrastructure Ransomware has evolved into a "Ransomware-as-a-Service" (RaaS) model. Groups like RansomHub, LockBit 3.0, and RansomEXX are devastating Indian networks. Recently, a misconfigured Jenkins server at a tech vendor led to a massive RansomEXX attack that severely disrupted India's banking ecosystem, proving that an enterprise is only as secure as its weakest third-party vendor.
The 2026 Mandate: How India Must Respond
The convergence of the WEF's strategic warnings and the DSCI's tactical data makes one thing clear: India cannot simply "firewall" its way out of this crisis.
At the Macro (Government) Level:
- Treat Information Integrity as National Security: As the WEF suggests, India must expand initiatives like the Election Commission's 'FACT Principle' and PM-DISHA. Combating deepfakes, AI-driven disinformation, and hybrid warfare requires a "Whole-of-Society" approach.
- Statutory Intelligence Fusion: To combat hybrid threats that blend physical terrorism with cyber-attacks, India needs real-time intelligence fusion through agencies like the Multi-Agency Centre and I4C (Indian Cyber Crime Coordination Centre).
At the Micro (Enterprise/CISO) Level:
- Assume Breach (Zero Trust): The perimeter is dead. CISOs must adopt a strict Zero Trust framework—continuous authentication, micro-segmentation, and rigorous access controls.
- AI vs. AI: With attackers using Generative AI to write polymorphic malware and perfect phishing emails, defenders must fight fire with fire. Investing in AI-enhanced Security Operations Centers (SOCs) and predictive threat intelligence is no longer optional.
- Secure the Cloud & Supply Chain: With 62% of attacks happening in the cloud, Cloud Security Posture Management (CSPM) and rigorous audits of third-party vendors must become standard operating procedure.
Conclusion
India's digital economy is projected to contribute 20% to its GDP by 2026. This digital wealth is exactly why the World Economic Forum ranks cybersecurity as the nation's greatest existential threat.
The data from the DSCI proves that the storm is already here. Hacktivists are probing our public utilities, state-sponsored APTs are lurking in our defense networks, and financial malware is sitting in the pockets of millions of citizens.
To secure its future as a global superpower, India must realize that in the 21st century, the strength of a nation is not just measured by its GDP or its military, but by the resilience of its digital infrastructure.