
The Quantum Heist: Defeating "Store Now, Decrypt Later" with Merkle Tree Certificates
State-sponsored hackers are hoarding encrypted data today to break it tomorrow. Here is how Google’s new Merkle Tree Certificates will stop them.
The cybersecurity landscape is currently hovering on the edge of a fundamental cryptographic paradigm shift. For decades, the internet has relied on classical cryptographic algorithms to secure communications, financial transactions, and classified state secrets. But a silent countdown has begun, driven by the rapid, inevitable advancement of quantum computing.
Recently, Google Chrome announced a massive, ecosystem-altering initiative to protect HTTPS connections from emerging quantum threats. Instead of simply patching the old system, Google, alongside the Internet Engineering Task Force (IETF) and its "PLANTS" working group, is building an entirely new cryptographic architecture: Merkle Tree Certificates (MTCs).
To understand why this is a revolutionary game-changer—and why traditional post-quantum solutions were doomed to break the internet—we must first examine the threat intelligence landscape from a cryptographic perspective. Why do we need this overhaul, what exactly is at risk, and who is already capitalizing on our current vulnerabilities?
The Cryptographic Divide: What Quantum Breaks (And What It Doesn't)
The fear surrounding quantum computing is not just theoretical hype; it is grounded in hard mathematics. Current internet security relies heavily on two types of encryption: symmetric and asymmetric.
Asymmetric Cryptography (Public Key Infrastructure): This includes RSA (Rivest-Shamir-Adleman), ECC (Elliptic Curve Cryptography), and Diffie-Hellman key exchanges. These algorithms protect the TLS handshakes that initiate secure HTTPS web traffic. They rely on complex mathematical problems—like integer factorization and discrete logarithms—that would take classical computers millions of years to solve.
Enter Shor’s Algorithm. A sufficiently powerful quantum computer running Shor’s Algorithm can solve these specific mathematical problems exponentially faster. Once a quantum computer reaches maturity, the entire public-key infrastructure of the modern web will be fundamentally broken. RSA and ECC will be rendered obsolete.
Symmetric Cryptography and Hashing: However, quantum computers are not magic keys to all encryption. Algorithms like AES (used for bulk data encryption) and Hash functions (like SHA-256) are fundamentally different. While a quantum algorithm known as Grover’s Algorithm can weaken them by speeding up brute-force attacks, it does not completely break them. The defense is simple: double the key size. An AES-256 bit key is considered highly quantum-resistant because Grover's Algorithm effectively reduces its strength to that of AES-128, which remains currently unbreakable.
The fatal vulnerability lies almost entirely in the asymmetric key exchange. If an adversary can break the asymmetric handshake using a quantum computer, they can extract the symmetric session keys—and thereby decrypt the entire conversation.
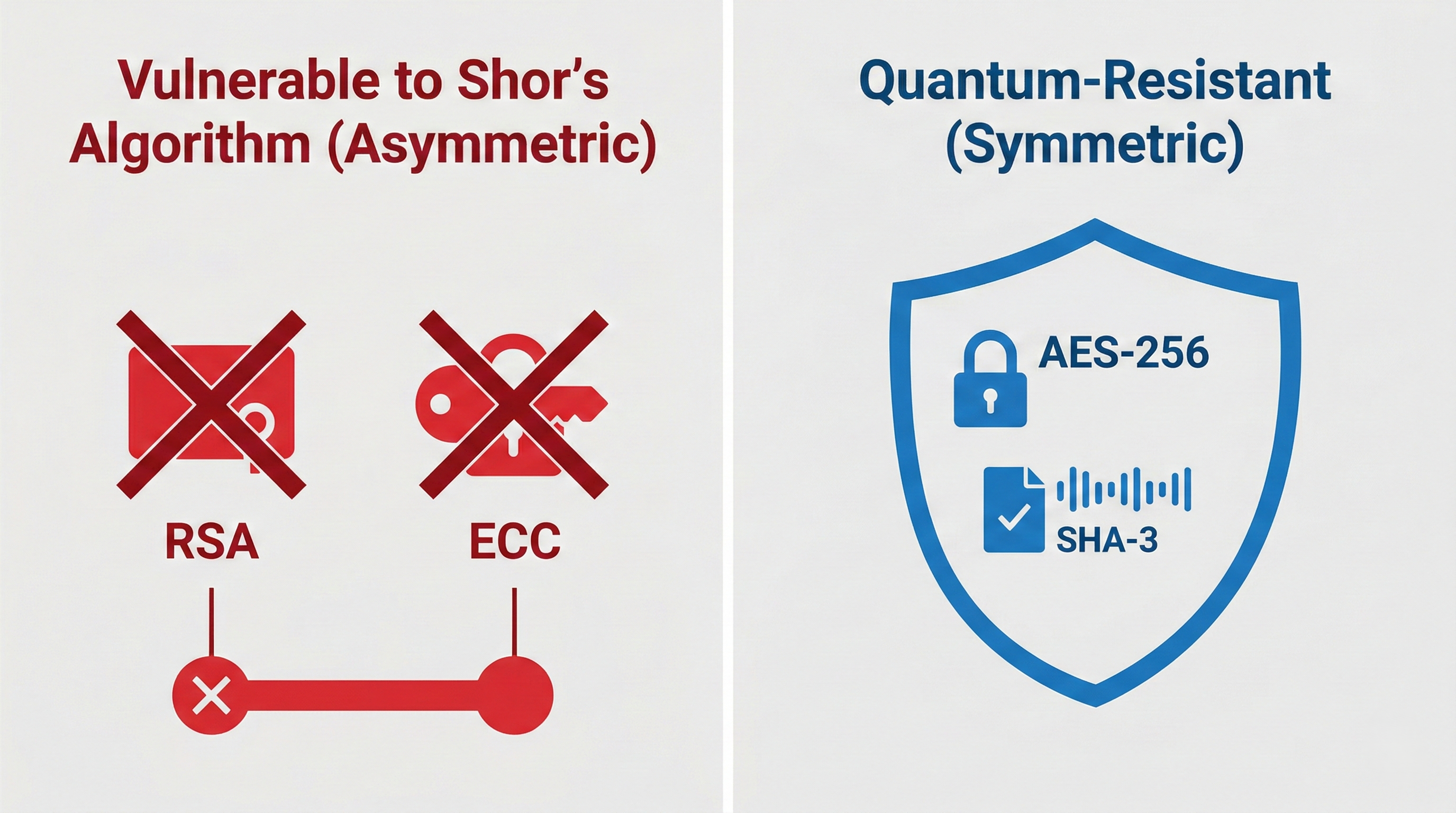 While symmetric encryption like AES-256 remains largely safe, the asymmetric algorithms (RSA/ECC) securing current TLS handshakes are critically vulnerable to quantum decryption.
While symmetric encryption like AES-256 remains largely safe, the asymmetric algorithms (RSA/ECC) securing current TLS handshakes are critically vulnerable to quantum decryption.
"Store Now, Decrypt Later": The Silent APT Campaign
If a quantum computer capable of breaking RSA does not exist yet, why is Google acting so aggressively now? The answer lies in the current Tactics, Techniques, and Procedures (TTPs) of highly advanced Advanced Persistent Threat (APT) groups.
Threat intelligence heavily monitors a strategy known as "Store Now, Decrypt Later" (SNDL), sometimes referred to as "Harvest Now, Decrypt Later." Nation-state actors, most notably state-sponsored groups operating out of China, as well as Russian intelligence and other global cyber-espionage units, are actively engaging in the mass interception and storage of encrypted internet traffic.
These APT groups are playing a long game. They are targeting highly sensitive communications: military intelligence, intellectual property, diplomatic cables, dissident communications, and proprietary corporate data. The premise is straightforward: while the APT group cannot read the TLS-encrypted data today, they are hoovering it up into massive state-funded data centers. They are simply downloading everything of value and patiently waiting for "Q-Day"—the day a Cryptographically Relevant Quantum Computer (CRQC) comes online.
Once that hardware is available, they will retroactively break the RSA/ECC handshakes of the stored data, extract the session keys, and read decades' worth of classified secrets. Because highly classified data has a long "shelf life" (a nuclear submarine schematic, a covert operative's identity, or an aerospace patent is still highly sensitive 10 to 15 years later), the threat of quantum computing is not a future problem. It is an active, ongoing data breach happening right now.
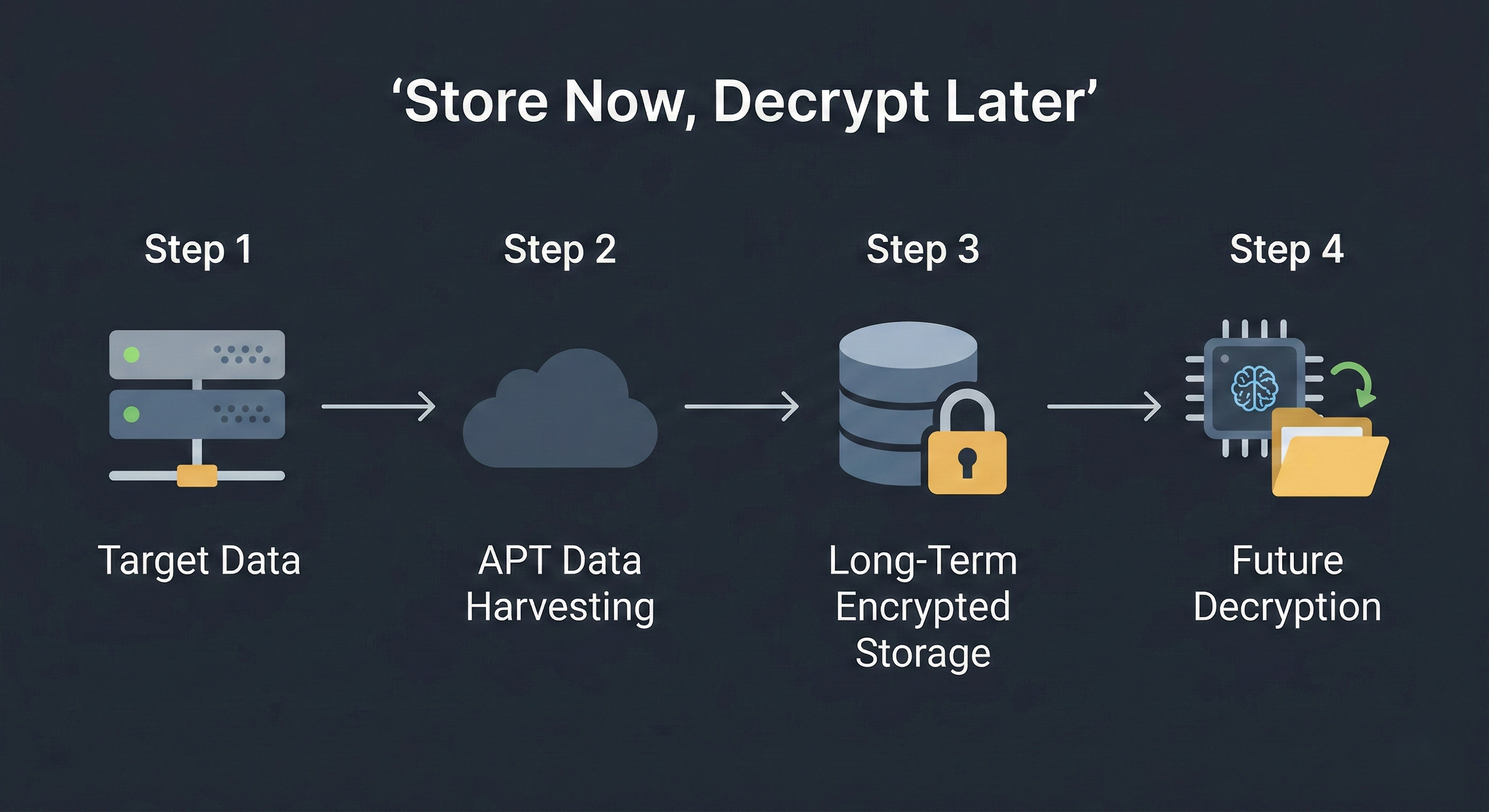 The SNDL attack chain: Threat actors bypass current decryption limitations by hoarding encrypted traffic today, relying on future quantum hardware for payload extraction.
The SNDL attack chain: Threat actors bypass current decryption limitations by hoarding encrypted traffic today, relying on future quantum hardware for payload extraction.
The Countdown to Q-Day: Qubits and Timelines
Exactly how much time do we have before these harvested datasets are cracked wide open? Threat analysts and quantum physicists measure this timeline in terms of "qubits" (quantum bits).
Current quantum computers are in the "NISQ" (Noisy Intermediate-Scale Quantum) era. They have a few hundred physical qubits, but they are highly prone to error due to environmental noise and interference. To break an RSA-2048 bit key, a quantum computer needs logical qubits—which are perfectly error-corrected and stable.
It is estimated that breaking RSA-2048 requires roughly 4,000 fault-tolerant logical qubits. Because error correction requires massive redundancy, generating a single logical qubit might require roughly 1,000 physical qubits. Therefore, a machine capable of breaking current internet encryption will likely require millions of physical qubits.
Currently, the most advanced quantum processors have just over 1,000 physical qubits. While we are still years away, aggressive state funding and technological breakthroughs mean threat intelligence agencies generally estimate "Q-Day" will arrive somewhere between 10 to 15 years from now (roughly 2035-2040). Given the shelf-life of sensitive data, the window to implement Post-Quantum Cryptography (PQC) across the internet is closing rapidly.
The X.509 Bottleneck: Why Traditional Fixes Fail
The obvious solution is to swap out vulnerable algorithms (RSA/ECC) for new, Post-Quantum Cryptography (PQC) algorithms that have been standardized by NIST.
However, applying this to the web's Public Key Infrastructure (PKI) creates a massive logistical nightmare. Traditional HTTPS relies on X.509 certificates. In a standard TLS handshake, the server sends a serialized chain of these certificates to the browser to prove its identity.
The problem? Post-quantum cryptographic signatures and public keys are massive compared to their classical counterparts. If we simply drop post-quantum keys into traditional X.509 certificate chains, the size of the data transmitted during every single web connection setup would skyrocket. This bandwidth bloat would cripple internet performance, causing severe latency issues, especially on mobile networks, IoT devices, or in developing regions. Furthermore, the overhead of current Certificate Transparency (CT) logging requirements would only compound the problem.
Google realized that trying to force massive post-quantum algorithms into the legacy X.509 framework was a dead end. Consequently, Chrome confirmed it will not add traditional X.509 certificates containing post-quantum cryptography to the Chrome Root Store.
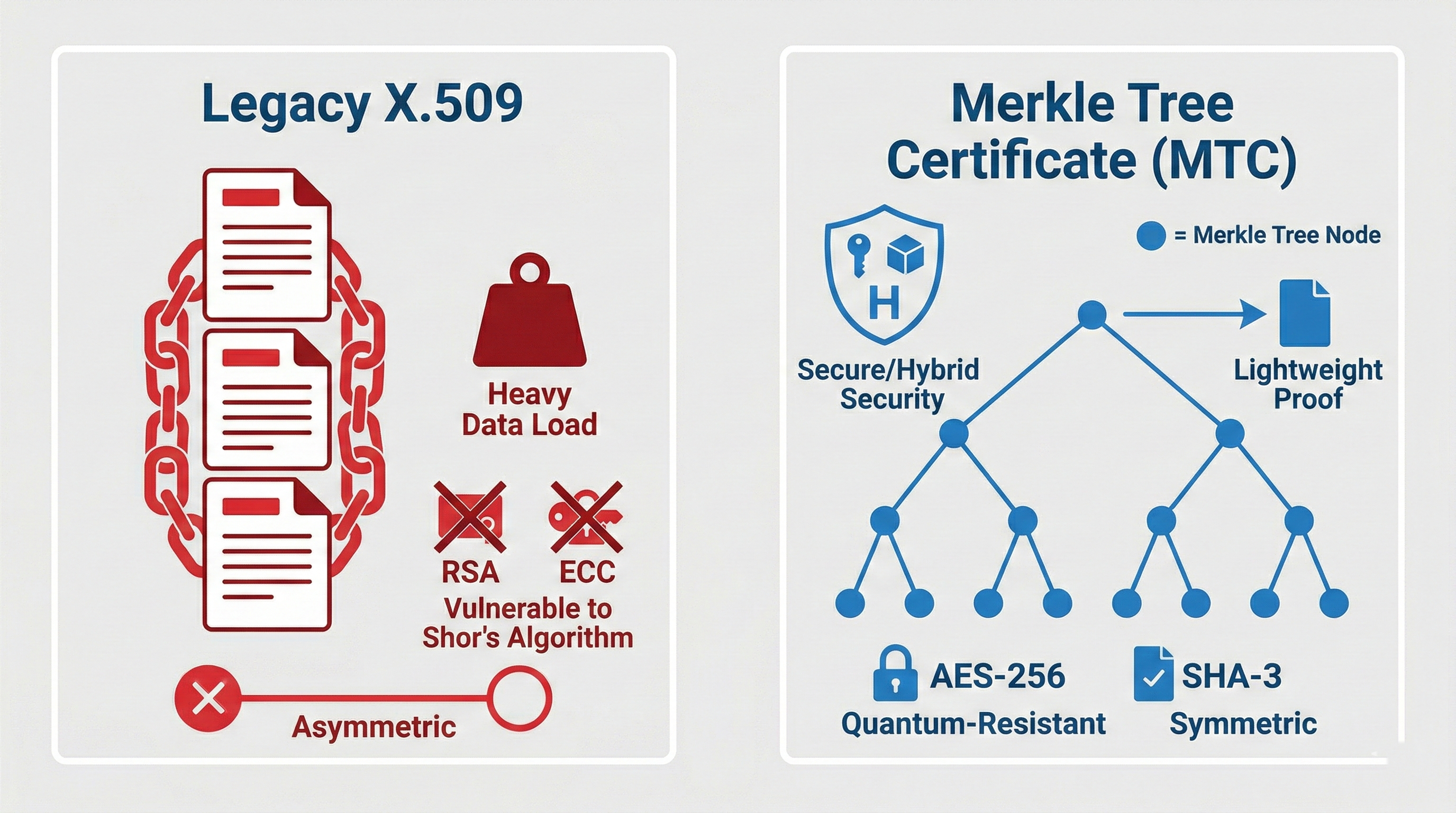 Legacy X.509 certificate chains incur massive bandwidth penalties when using post-quantum cryptography. MTCs solve this by transmitting only lightweight mathematical proofs.
Legacy X.509 certificate chains incur massive bandwidth penalties when using post-quantum cryptography. MTCs solve this by transmitting only lightweight mathematical proofs.
Google's Silver Bullet: Merkle Tree Certificates (MTCs)
To shield HTTPS against quantum threats without destroying internet speeds, Google—along with Cloudflare and the IETF—has engineered an elegant solution: Merkle Tree Certificates (MTCs).
MTCs represent a total evolution of how web identity and encryption will be handled. Instead of sending a heavy, serialized chain of post-quantum signatures to the user's browser, MTCs utilize compact cryptographic proofs based on Merkle Trees (a mathematical structure used to efficiently verify large sets of data).
Here is how MTCs serve as a game-changer:
- The Tree Head: Instead of a Certificate Authority (CA) individually signing every single website certificate with a massive post-quantum key, the CA signs a single, collective "Tree Head." This single signature represents a Merkle Tree that can contain millions of individual website certificates.
- Lightweight Proofs: When your Chrome browser connects to a website, the server no longer sends a heavy certificate chain. Instead, it sends a tiny, lightweight "proof of inclusion"—a mathematical confirmation that the website's specific certificate exists within that securely signed public tree.
- Decoupling Size from Security: MTCs decouple the security strength of the algorithm from the size of the data transmitted. You get the unbreakable security of post-quantum cryptography with a TLS handshake that is as fast, or faster, than the internet we use today.
- Embedded Transparency: With MTCs, transparency is built-in by default. It is mathematically impossible to issue an MTC without including it in the public tree. This prevents rogue CAs or state actors from secretly issuing fraudulent certificates to conduct Man-in-the-Middle (MitM) attacks.
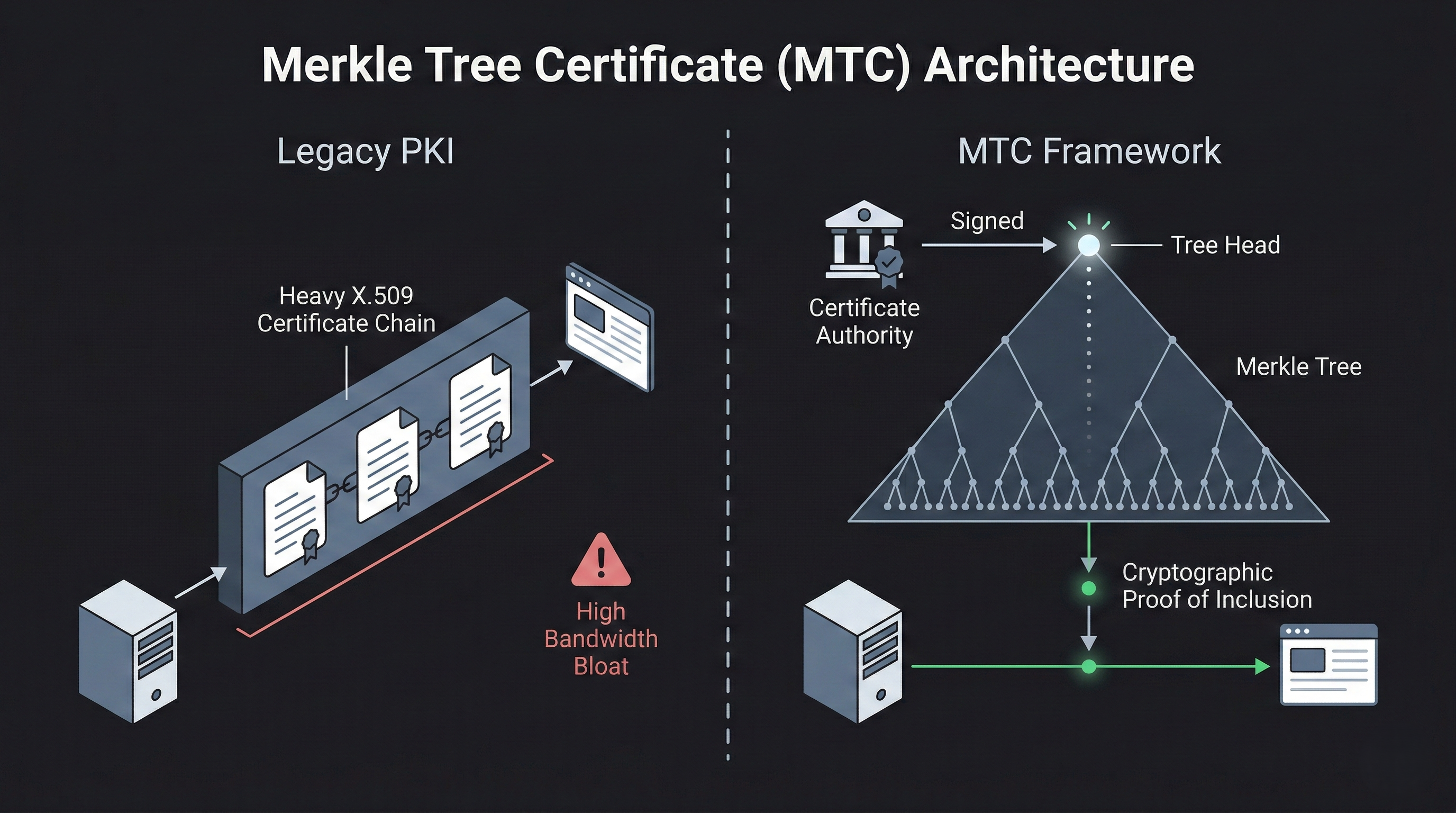 A visual comparison showing how MTCs replace heavy, bandwidth-clogging certificate chains with lightweight cryptographic proofs, enabling quantum security without sacrificing speed.
A visual comparison showing how MTCs replace heavy, bandwidth-clogging certificate chains with lightweight cryptographic proofs, enabling quantum security without sacrificing speed.
Defeating SNDL and The Rollout Strategy
By transitioning to MTCs, the web ecosystem effectively neutralizes the "Store Now, Decrypt Later" threat matrix. When MTCs are deployed alongside post-quantum key encapsulation mechanisms, the session keys negotiated during the TLS handshake become entirely immune to Shor's Algorithm.
If a Chinese APT group intercepts an MTC-secured HTTPS connection in 2027 and stores it in a data center, it will be utterly useless. Even when they spin up a 10,000-logical-qubit computer in 2038, the underlying mathematics of the post-quantum MTC handshake will hold firm. The harvested data remains permanently unreadable.
Google is not treating this as a theoretical concept; they have laid out a concrete, three-phase operational timeline:
- Phase 1 (Underway): Google and Cloudflare are conducting real-world feasibility studies, testing MTCs using live internet traffic. To prevent user disruption, these experimental MTC connections are currently backed by traditional X.509 certificates as a fail-safe.
- Phase 2 (Q1 2027): Google will invite established Certificate Transparency (CT) Log operators to bootstrap public MTC infrastructure. These operators already possess the high-availability infrastructure required to scale MTC deployment rapidly.
- Phase 3 (Q3 2027): The launch of the Chrome Quantum-resistant Root Store (CQRS). This new, purpose-built trust store will only support MTCs. It will operate alongside the legacy Root Program to manage the transition, but the message is clear: the future of secure web browsing belongs exclusively to Merkle Trees.
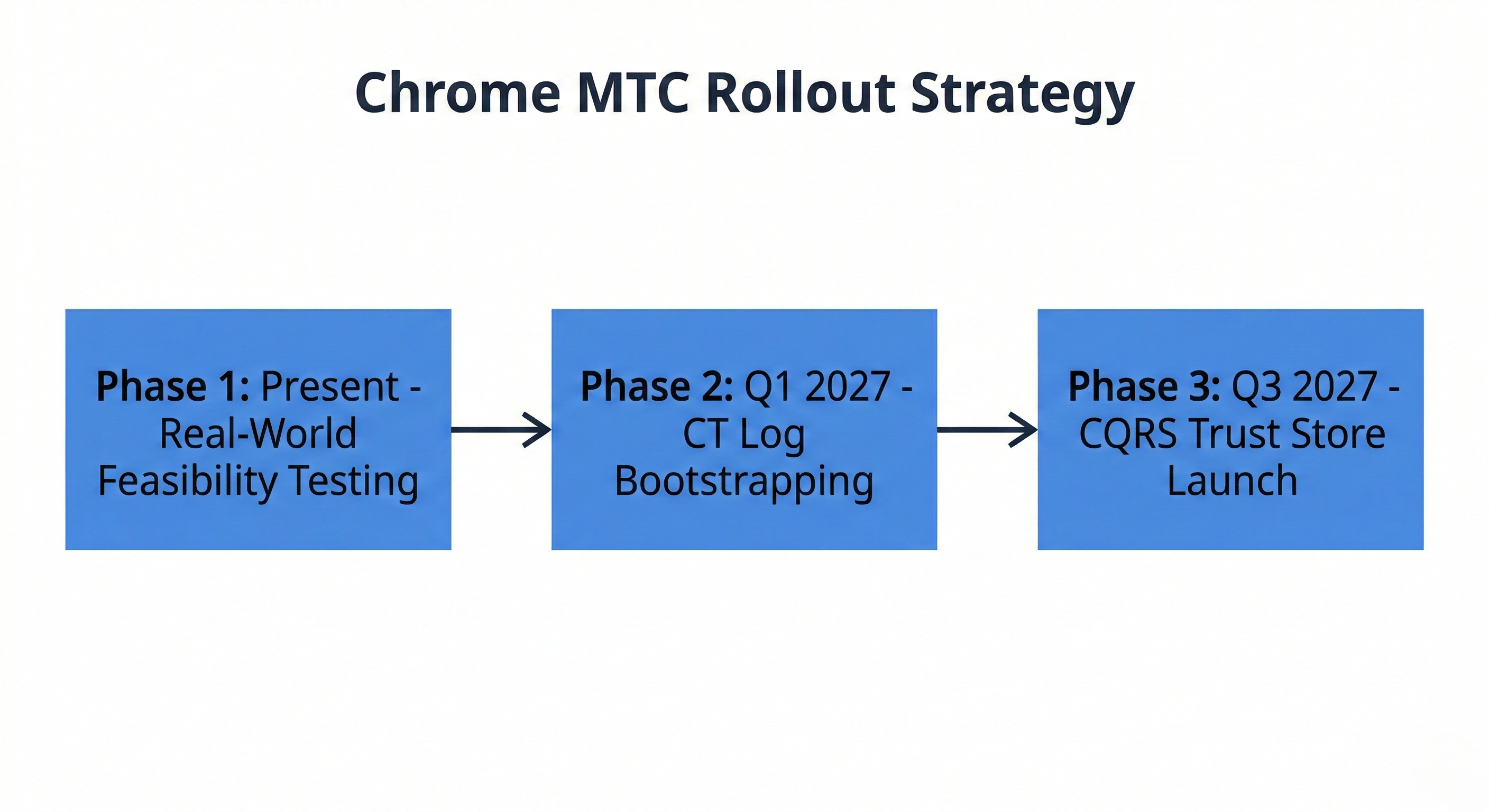 Google’s aggressive rollout strategy ensures that a purpose-built, quantum-resistant infrastructure will be actively natively supported by Chrome by Q3 2027.
Google’s aggressive rollout strategy ensures that a purpose-built, quantum-resistant infrastructure will be actively natively supported by Chrome by Q3 2027.
Conclusion
The transition to Merkle Tree Certificates is one of the most significant architectural upgrades to internet infrastructure since the widespread adoption of HTTPS itself. From a threat intelligence perspective, it acts as a decisive, systemic countermeasure against state-sponsored "Store Now, Decrypt Later" espionage campaigns.
By abandoning the legacy constraints of X.509 certificates and prioritizing cryptographic agility, embedded transparency, and lightweight data transmission, Google and the IETF are hardening the web's defenses before the threat fully materializes. When Q-Day finally arrives, the internet's perimeter will hold.